How to Buy Tesla Stock
Tesla is more than a car manufacturer, it is one of the most innovative and interesting companies in the world, armed with a vision that is similar to Ford in the early decades of the previous century and Apple Computers in the 70s. It’s not surprising that many investors around the world have a special interest in the company, its stock, and its CEO. Of course, we cannot mention Tesla without mentioning its CEO, and founder, Elon Musk.
Tesla is an American company involved in manufacturing electric vehicles, solar panels, and provide clean energy solutions. Given Tesla’s success so far, the company attracts lots of attention from the media and has a large number of dedicated fans. As a result, Tesla’s stock price has been on a wild ride since its initial public offering on June 29, 2010.
Tesla is considered by many to be ahead of competitors in the industry in many regards. The company is leading the race toward building the first fully self-driving electric car but is also known for bringing clean energy technologies such as sustainable electric batteries and clean energy storage.
In this article, we review three popular brokers from whom you can buy Tesla stocks.
-
-
Where to Buy Tesla Stock?
Tesla is listed on the NASDAQ exchange, which means you’ll have to find a broker that connects you to the exchange or an online CFD broker that makes it possible to speculate on Tesla’s stock price. Therefore, before you can buy Tesla stock, you’ll need to open a trading account with a licensed regulated online stock broker. Below, we have the top three brokers that currently offer Tesla stock.
RECOMMENDED BROKER
What we like
- 0% Commission
- Trade Stocks Via CFDs
- Authorized & regulated by the FCA
Min Deposit
$100
Charge per Trade
Zero Commission
Available Assets
- Total Number of Stocks & Shares+2000
- US Stocks
- German Stocks
- UK Stocks
- European
- ETF Stocks
- IPO
- Funds
- Bonds
- Options
- Future
- CFDs
- Crypto
Charge per Trade
- FTSE 100 Zero Commission
- NASDAQ Zero Commission
- Dax Zero Commission
- Facebook Zero Commission
- Alphabet Zero Commission
- Tesla Zero Commission
- Apple Zero Commission
- Microsoft Zero Commission
Deposit Method
- Wire transfer
- Credit Cards
- Bank Account
- Paypal
- Skrill
How to Buy Tesla Stock
There is quite a large number of brokers that allow you to buy Tesla.
There are a few simple steps you should follow to complete your first Tesla stock purchase. Keep in mind that you can also short-sell the Tesla stock and make a profit from a decline in the stock price.
Step 1: Search for Tesla stocks
Assuming that you have completed the account creation process, the next step involves logging into the trading platform and find Tesla stock. Simply type ‘Tesla’ or ‘TSLA’ at the search bar and click on the trade ‘Trade’ button.
As you can see, on the Tesla stock page, you will be able to get access to the price chart, important stats about the stock, Twitter feed, and research tools such as market sentiment, analyst recommendations, and more.
Step 2: Click on ‘Trade’
Once you are ready to buy (or short-sell) Tesla, click on the ‘Trade’ button.
Step 3: Set-Up a Market Order and Buy Tesla Stock
Next, you’ll have to insert the necessary parameters in order to send an order to the market. These include the amount you want to invest in the trade, the order type (market order/limit order), the leverage ratio, and the stop-loss and take-profit orders.
Click the ‘Set Order’ button to complete your order.
Why Invest in Tesla?
A Long Term Vision
Over the past few years, Tesla has outlined its goals and convinced many that the company’s vision is different than most companies out there. Obviously, Elon Musk has contributed to forming Tesla’s vision. Since its foundation in 2003, Tesla’s main goal has been to speed up the world’s transition to a sustainable clean energy future including electric cars, solar panels, and producing clean energy solutions.
Model Y and Cybertruck
The upcoming Model Y and Cybertruck models are expected to push Tesla one step forward. Although the futuristic-like Cybertruck has been called by some as one of the ‘ugliest’ cars ever made, others believe that the Cybertruck is revolutionary. So far, the estimations for pre-orders of the Cybertruck stands on around 535,000.
The Model Y is expected to be Tesla’s top seller in 2020 as well as in the upcoming years.
Tesla Self-Driving Autonomous Cars
Autonomous vehicles may be a significant part of the future. The only question, who might be the first to sell these cars to retail clients. It might be Tesla. In fact, Tesla is one of the top car manufacturer or tech companies to lead the race, most likely following Waymo of Google and General Motors Cruise vehicle.
Tesla’s vehicles should be able to achieve full self-driving capabilities within the next few years. Meanwhile, Tesla develops advanced self-driving features such as the Advanced Sensor Coverage, neural net for vision, sonar and radar processing software, and the autopilot advanced safety and convenience features.
About Tesla Stock
Tesla Company Background
Tesla was founded on July 1, 2003, in San Carlos, California, United States by Martin Eberhard and Marc Tarpenningn who believed that effective electric vehicles can replace traditional gasoline cars. Originally, the company was named Tesla Motors after the famous inventor and electrical engineer Nikola Tesla, and only changed its name to Tesla Inc in 2017.
In 2004, Elon Musk has joined the company and became the chairman of Tesla Board of Directors after investing 30 million dollars. Since then, Elon Musk is the face of Tesla and considered by many to be one of the most influential minds of this century. Musk also gets a constant comparison to Steve Jobs, Bill Gates, and Henry Ford.
The Roadster was the first vehicle Tesla has manufactured and was sold to the public from 2008 to 2012. However, Tesla was not a successful company at that time and its IPO in 2010 was a savior for the company after Tesla has raised $226 million. The Model S was the next car Tesla has produced and marked the beginning of the success of the company. Since then, Tesla has expanded the range of products. In 2012, Tesla introduced the Supercharger network – freestanding charging stations for Tesla Motor vehicle and Casino Utan Svensk Licens owners. At the time of writing, the company operates around 12,000 superchargers at 1,400 stations worldwide.
Apart from Tesla electric cars and the Supercharge network, Tesla has expanded its services to solar energy products like solar roofs, solar panels, electric batteries, and clean energy storage. In 2019, Tesla unveiled the CyberTruck, the first pickup truck made by Tesla with an exterior shell and ultimate protection for passengers.
Tesla Stock
Remarkably, Tesla’s stock has doubled its price since a sharp drop in March that was likely to be caused by the Coronavirus pandemic. On March 18, 2020, Tesla shares fell to around $360 before rebounding all the way back up to $780. Tesla stock has reached an all-time high of $901 on February 21, 2020, and currently, analysts’ ratings are mixed between “buy” and “hold” with price targets are ranging from $440 to $925.
More importantly, Tesla has recently released its Q1 2020 earnings report and for the first time since its foundation, the company reports a Q1 profit of $16M. Furthermore, Tesla has ended the first quarter of 2020 with $8 billion in cash, a rise from $6.3 billion at the end of 2019. In a way, 2020 so far signals the continuation of Tesla’s extraordinary growth in 2019.
The technical analysis of Tesla’s stock signals a ‘buy’ and ‘strong buy’ recommendation, mainly due to the latest surge in price since March.
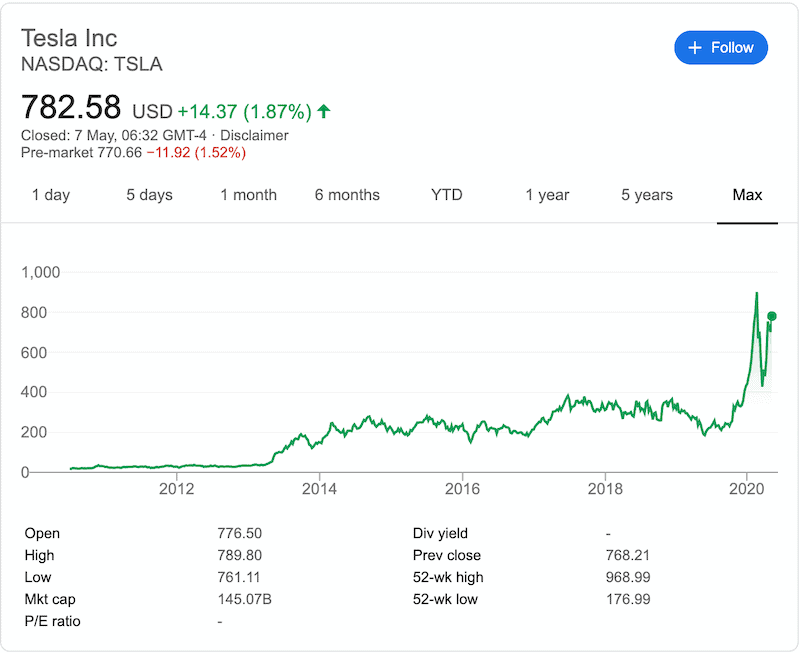
The Tesla stock is very volatile and unpredictable. Unlike other stocks that can be valued on fundamentals with more clarity, Tesla stock has a price movement that is similar to extremely volatile assets such as bitcoin and Apple stock.
Tesla has a market capitalization of around $144 billion, which makes Tesla bigger than Ford Motor Co., Honda, and General Motors all together.
85% of the company’s annual revenue comes from the sale of electric vehicles, which means that Tesla is mostly dependent on car sales to generate revenues. Globally, Tesla sold between 367,000 and 368,000 electric vehicles in 2019, making Tesla the leading electric vehicle producer in the world.
But one thing is for sure, Tesla has a quite significant advantage over its competitors when it comes to battery technology. Tesla’s batteries are much more effective and bigger than those of other manufacturers, whether the batteries are used for electric vehicles or clean solar panels. Moreover, some experts say that Tesla’s electronic components and technology are ahead of any competitor in the industry.
Generally speaking, Tesla’s stock is a phenomenon and should be on your watchlist at all times. Right now, Tesla stock is not so far from its all-time high, which wasn’t that long ago, and with the recent positive reports and the hopes of an economic recovery, Tesla’s stock has the potential to continue trading above its all-time-high record. As of Nov 5, 2020 – analysts are forecasting a 12 month price target of $355.60 per share for Tesla stock.
Conclusion
Tesla is the largest electric vehicle company in the world and is on the race to become the first company to release an autonomous self-driving car to retail clients. Moreover, Tesla has a unique vision and an approach that might solve some of the most serious issues currently threatening humanity such as the shortage of fossil fuels and climate change.
FAQs
How much were Tesla stocks originally?
Tesla went pubic on June 29, 2010, and offered 13,300,000 shares of common stock at a price of $17 per share.
How much could you make if you have invested $1,000 in Tesla’s IPO?
Investors who have invested $1000 in Tesla at its IPO could make a profit of $44,703 at the current price of $780.04.
What is the ticker symbol for Tesla stock?
Tesla stock is listed on the NASDAQ stock exchange and is traded under the ticker symbol ‘TSLA.’
Does Tesla pay dividends?
No, Tesla has never paid dividends to its shareholders nor the company anticipates to pay dividends in the near future, which is a typical business structure for companies that are built on long-term growth.
Is Tesla a profitable company?
Tesla has never had a profitable year yet but the company finished 2019 with back-to-back profitable quarters and announced a profit in the first quarter of 2020 of $16 million.
What is the market cap of Tesla?
At the time of writing, the market capitalization of Tesla is around $144.6B.
See Our Full Range of Stock Buying Resources
Tom Chen
View all posts by Tom ChenTom is an experienced financial analyst and a former derivatives day trader specialising in futures, commodities, forex and cryptocurrency. He has a B.A. in Economics and Management and his work has been published on a range of publications, including Yahoo Finance, FXEmpire and NASDAQ.com.
WARNING: The content on this site should not be considered investment advice. Investing is speculative. When investing your capital is at risk. This site is not intended for use in jurisdictions in which the trading or investments described are prohibited and should only be used by such persons and in such ways as are legally permitted. Your investment may not qualify for investor protection in your country or state of residence, so please conduct your own due diligence. Contracts for Difference (“CFDs”) are leveraged products and carry a significant risk of loss to your capital. Please ensure you fully understand the risks and seek independent advice. This website is free for you to use but we may receive commission from the companies we feature on this site.
Copyright © 2025 | Learnbonds.com



